Financial fraud methods are becoming more sophisticated and the techniques to combat such attacks also need to evolve. Financial institutions have been investing on preventing and combating fraudulent attacks but the extent and nature of financial fraud continues to change. While eliminating financial frauds is not a practical goal, there is a need to evolve the ways fraudulent attacks are dealt. Clearly, the paradigm needs to change and big data, it appears, is a novel and potentially potent weapon. Big data has brought with it novel fraud detection and prevention techniques such as behavioral analysis and real-time detection to give fraud fighting techniques a new perspective. Analytics allow financial institutions to gain a deeper understanding of suspicious activities, derive patterns and locate unusual transactions that are helpful in preventing fraud. Financial institutions are slowly waking up to the new ways of fighting fraud.
Extent of financial fraud
Experian, a reputed global information services company conducted a survey in 2014 on financial fraud. Experian’s fraud report 2014 lists the top trends in fraud across the globe. The trends give an idea of how the fraudulent attacks have been evolving. Here are some of the salient findings from the report.
- The rate of detected frauds has increased from 24 to 35 frauds per 10000 applications. So, data and identity are becoming increasingly more vulnerable.
- Of all types of fraud, identity theft has increased at the fastest rate. From 30% in 2013, incidents of identity theft has risen to 47% in 2014.
- Third-party involvement was the most notable finding in frauds related to cards, loans and savings products.
- Mortgage application frauds accounted for the highest among all detected frauds. In August 2013, 82 of every 10000 mortgage applications were found fraudulent.
- Current account application fraud increased by 60% from August 2013 to August 2014.
- Third-party involvements have been on the rise in the case of all types of frauds. Since August 2014, third-party involvements accounted for 79% of all fraud discoveries.
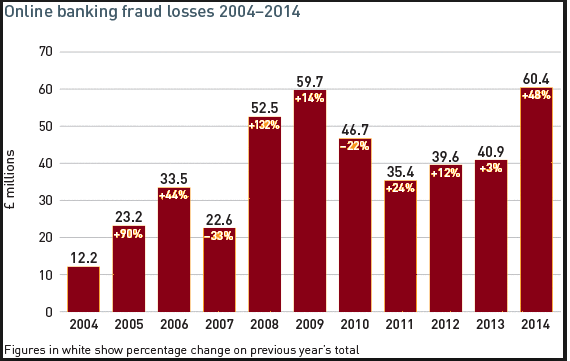
Following image shows the online banking fraud losses between 2004 and 2014.
Image1: Trends in online banking fraud losses
(Source: http://www.theukcardsassociation.org.uk/plastic_fraud_figures/)
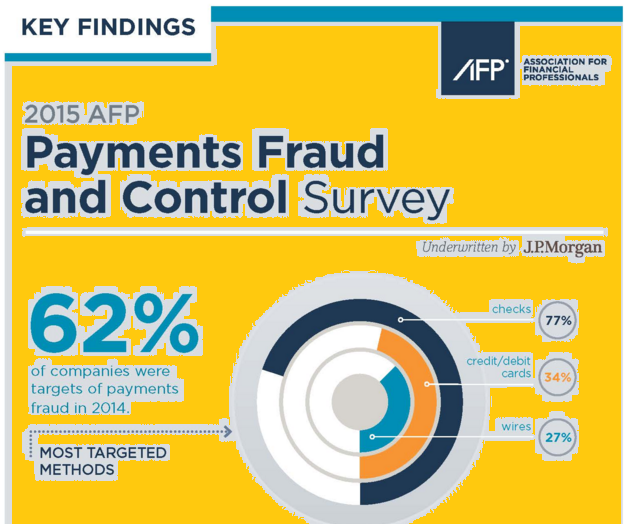
According to AFPs (Association for Financial Professional) payments fraud and control survey, following image shows the statistics for payment frauds in 2015.
Image2: Payment fraud statistics in 2015
(Source: http://www.afponline.org/fraud/)
Novelty in financial fraud techniques
Change has been the only constant when it comes to finding novel ways to fraud. Fraudsters have been constantly finding smarter, quicker and innovative ways to steal identity and data. The first step to combating such fraud is to accept that there will constantly be new ways of attacks. The section below provides a case study on how a highly sophisticated phishing attack, which the Federal Bureau of Investigation (FBI) dubbed as business email compromise, resulted in a loss of millions of dollars.
The phishing attack claimed victims who were the employees of a number of large corporations in the US. The attackers would first do a reconnaissance of the executives who dealt with large payments, wire transfers and bank accounts. Secondly, the attackers would spoof top executives with financial decision-making powers and obtain their email credentials. Third, the attackers would send emails from the executive’s account to persons dealing in large payments asking them to transfer large sums of money to an account controlled by the attackers. As a result, Ubiquiti Networks lost $46.7 million; Crelan Bank in Belgium bled $75.8 million and FACC A.G, a Boeing supplier, aircraft component manufacturer, lost $54.5 million.
An FBI advisory stated how chilling and clinical the attack was, “The accountant for a U.S. company recently received an e-mail from her chief executive, who was on vacation out of the country, requesting a transfer of funds on a time-sensitive acquisition that required completion by the end of the day. The CEO said a lawyer would contact the accountant to provide further details. It was not unusual for me to receive e-mails requesting a transfer of funds,” the accountant later wrote, and when she was contacted by the lawyer via e-mail, she noted the appropriate letter of authorization—including her CEO’s signature over the company’s seal—and followed the instructions to wire more than $737,000 to a bank in China.”
Obviously, to handle such sophisticated attacks, you need a different perspective of defense.
Big data provides a potential answer
Big data allows financial institutions to approach fraud differently and possibly get different results. Here is how big data can help.
Identify suspicious activities before damage is done
Banks continuously look for suspicious or unusual behavior represented by data in real time. For example, when a credit card holder performs transactions from a device for the first time, it sends a notification to the bank. If several transactions take place from different devices during a day, the data generated is a reasonable justification to raise an alarm. Banks are known to inform the valid card holders immediately and even block online transactions. Big data is making detecting unusual transactions easier. For example, if two transactions from the same credit card take place at different cities within a short time gap, the bank is going to get red flags.
Leverage data to detect suspicious activities
Banks access huge customer data from different sources such as social media, logs and call center conversation and that data can be potentially helpful in identifying abnormal activities. For example, when a credit card holder is travelling by an airplane and posts the status on Facebook, any credit card transaction during that period is abnormal and the bank can block the transaction.
Identify possible fraud attempts
Let us take the case of insurance industry that accepts a lot of fraudulent claims and even approves some. How can big data help solve this problem? The insurance industry can access data from a variety of sources such as social media, past claim records, criminal records, and phone records. When a claim is received, the insurer needs to scrutinize the claim beyond just the claim details. It should scrutinize the information of the claimant. If it detects anything suspicious with the claimant record, it should flag the claim for further investigation.
Case study of Alibaba
Alibaba, the Chinese ecommerce company, has been using big data effectively to tackle fraud. At Alibaba, any potential fraudster has to pass through 5 stages of verification which is a tough proposition. These five stages are (1) Account Check, (2) Device Check, (3) Activity Check, (4) Risk Strategy and (5) Manual Review. Each layer involves the use of huge amounts of data related to the seller and activities. For example, in the first layer of verification, several questions may be asked such as previous record in retailing, suspicious activity and so on. The second layer scrutinizes the devices such as the IP and device operations, number of devices the seller is possibly going to use and so on.
Summary
Using big data provides banks and finance companies the opportunity to prevent fraud to a large extent. However, the usage of big data for this purpose is till at its early stages and a lot needs to be done in this regard. Using big data requires a huge mindset change and that, according to Gartner’s Chuvakin, the companies need to “Learn to be data-centric and data-driven and then solve problems that call for bigger data, such culture change has to happen for the big data approaches to become pervasive across the industry. And yes, this includes willingness to explore, follow leads, and occasionally arrive at dead ends and algorithms that don’t work.“